Let's start with what Canvas actually is, because not everyone outside of education knows the name. Canvas is the learning management system used by 41% of universities and colleges in North America — and a significant chunk of K-12 schools too. It's where grades live. Where assignments get submitted. Where lecture videos are stored. And where students and teachers have private conversations they reasonably expected to stay private.
ShinyHunters didn't breach a peripheral system. They breached the platform where a generation of students does their schoolwork, and they did it quietly enough that Instructure — the company that runs Canvas — didn't notice until April 25, at which point the data was already gone.
How it unfolded — day by day
TimelineWho ShinyHunters actually are — and why the profile matters
Threat actorThreat analyst Luke Connolly at Emisoft describes ShinyHunters as a loose group of teenagers and young adults based primarily in the US and UK. That profile surprises people every time, because the scale of damage is genuinely extraordinary. Ticketmaster. Salesforce and dozens of its enterprise customers. Individual Ivy League universities. And now the biggest education platform in North America.
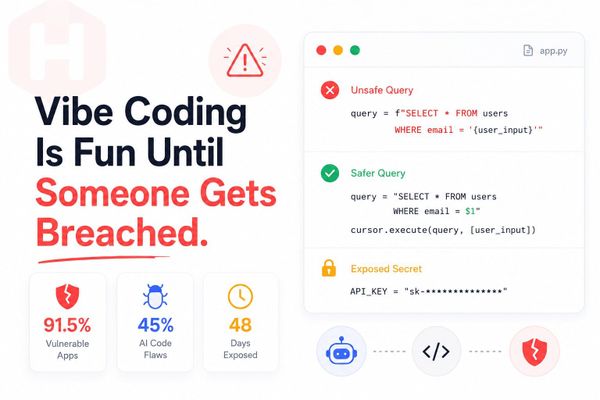
The strategy is not complicated, which is part of why it keeps working. Don't target the individual school. Target the platform that runs underneath 8,000 schools at once. The technical effort is the same, but the leverage is completely different. One successful breach of Instructure is a breach of Harvard, Penn, Duke, Wake County schools, and 8,806 other institutions simultaneously. The ransom negotiation happens with one company, but the threat covers everyone.
This is also not the first time ShinyHunters has hit education technology. Last autumn they breached Salesforce and claimed one billion records across dozens of companies — Instructure was one of the named victims then too. The group has been targeting this sector repeatedly, successfully, and apparently without sufficient consequence to deter them.
What 275 million Canvas records actually contains
The dataThe number is big enough to become abstract. What makes it concrete is thinking about what Canvas stores for a typical student.
Your grades. Every assignment you've submitted. Every piece of feedback a teacher gave you privately. Every direct message you've sent to a professor about struggling with coursework, requesting an extension, or discussing something you didn't want anyone else to see. Every message you've sent to a classmate through the platform. Course notes, lecture videos, your participation history.
Now multiply that by 275 million people. A lot of those people are minors — Canvas is used in K-12 schools, not just universities. Children's private messages. Student IDs. Academic records. All of it now in the hands of a group that has a history of publishing data when their demands aren't met.
What to actually do — students, parents, and IT teams
Action guideThe data has already been taken. Nothing changes that. What you can control is whether stolen credentials get used against you next.
Students and parents
IT and security teams
The May 12 deadline is four days away. We'll update this article as the situation develops — whether Instructure pays, whether data gets published, and what affected institutions are telling their students.
If you're a student, a parent, or work in education IT and your institution is on the list: the data is already gone. The question now is what happens next, and whether you've made it harder for stolen credentials to be used against you before you find out.
Check your institution's SSL certificate → Our free SSL Checker verifies any domain's certificate in seconds. No signup, nothing uploaded.
Check SSL Now